Portfolio
HydraVision
HydraVision is a Security Test Environment that enables global collaboration while ensuring compliance with industry standards like UNECE R155, ISO/SAE 21434, and GB 44495. Available as a Platform-as-a-Service and an On-Premise, HydraVision integrates automated security testing into product development lifecycles mandated by these regulations. Offering ultimate flexibility and control, it allows organizations to adapt swiftly to new vulnerabilities and evolving compliance requirements.
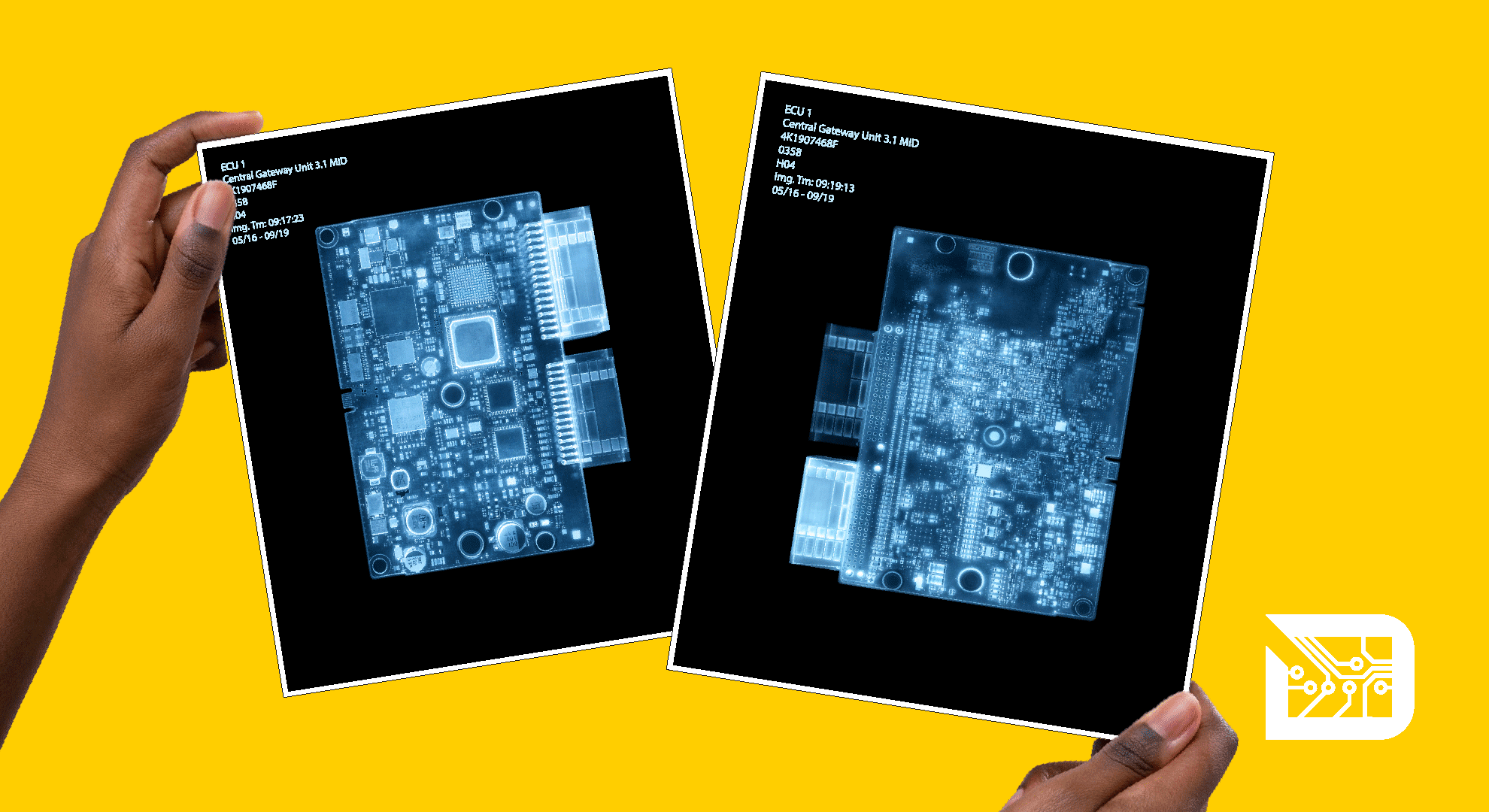
Hardware
Our security testing ecosystem is reinforced by purpose-built hardware solutions that enhance cybersecurity validation:
HydraLink – Versatile USB to Automotive Ethernet Interface supporting the 1000BASE-T1 standard.
HydraProbe – Security Test Tool integral to our HydraVision security test environment.
HydraHat – Dual CAN FD to Ethernet Gateway providing reliable and efficient data communication.
Cybersecurity Workshops
Mastering cybersecurity requires hands-on experience. Our workshops provide professionals with practical skills in reverse engineering, protocol analysis, and attack simulation – all the way up to hacking real vehicles and control units. With over nine years of industry expertise, our training equips engineers to navigate the complexities of embedded system security through real-world exercises and expert insights.
References
Your Benefits
Compliant

Each industry has its own standards. As new vulnerabilities emerge, our cybersecurity validation tools enable you to instantly adapt to the latest CVEs. Our automated, traceable tests ensure your embedded systems remain compliant with current regulations, providing comprehensive security vulnerability testing that scales with your needs.
Transparent

Years of R&D have enabled us to create a testing system that delivers clear, consistent, and reliable results. Our standardized approach ensures transparency, giving you full visibility and control over your network security test results. With global collaboration features and seamless on/offboarding, your team can effortlessly work together from anywhere in the world.
Cost-Effective

Our Security Test Environment is a Platform as a Service (PaaS) that merges decades of expertise with advanced technology to deliver cost-effective and efficient security testing. Unlike costly Hardware-in-the-Loop (HIL) setups or unsustainable one-time penetration tests, our automated solution ensures high-quality security testing while keeping costs low.
Join us @ ScapyCon
ScapyCon is our annual event where we bring together an engaged community of cybersecurity aficionados – pushing the boundaries of network packet manipulation across automotive, IoT, aviation, defense and beyond. At its core, ScapyCon is about technical expertise and shared knowledge – because only through collaboration can we advance security in the long run. Learn more